Posted in : Microsoft, Other, Virtual Apps and Desktops, Windows Server Av Stina Perbo Översätt med Google ⟶
7 years ago
Typically users get their printers mapped by Group Policies or Group Policy Preferences. Especially in Citrix environments, users should not have the right to add their own printers or drivers that are not approved for multi-user environments. On July 12th 2016, Microsoft released a security update (KB3170455) to safeguard Man-in-the-Middle (MITM) attacks for clients and print servers. Then an updated version was released again September 12th 2017.
Users could encounter the dialog boxes below if the driver did not meet the requirements of Microsoft where the driver would be packaged and signed with a certificate:
Scenario 1
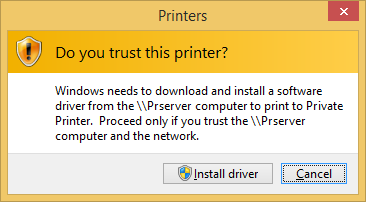
For non-package-aware v3 printer drivers, the following warning message may be displayed when users try to connect to point-and-print printers:
Scenario 2
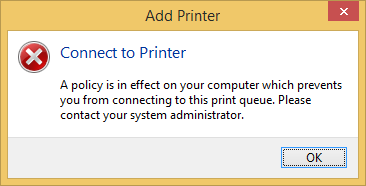
Package-aware drivers must be signed with a trusted certificate. The verification process checks whether all the files that are included in the driver are hashed in the catalog. If that verification fails, the driver is deemed untrustworthy. In this situation, driver installation is blocked, and the following warning message is displayed:
Even if you enabled Point and Print restrictions in GPO and specified which server’s clients could get drivers from, users could encounter an installation prompt and request administrator privileges to install.
For most printers this is not an issue if there is an up-to-date driver which is compliant. Some manufacturers do not always provide printers drivers that is both packaged and signed. The first thing you should do is update the driver to one that both is signed and packaged. Usually the drivers from the manufacturer are signed according to Microsoft Windows Hardware Quality Labs (WHQL) but may not be packaged correctly and the users get prompted for administrator credentials when the printer is being added to the client computer or in the remote desktop session.
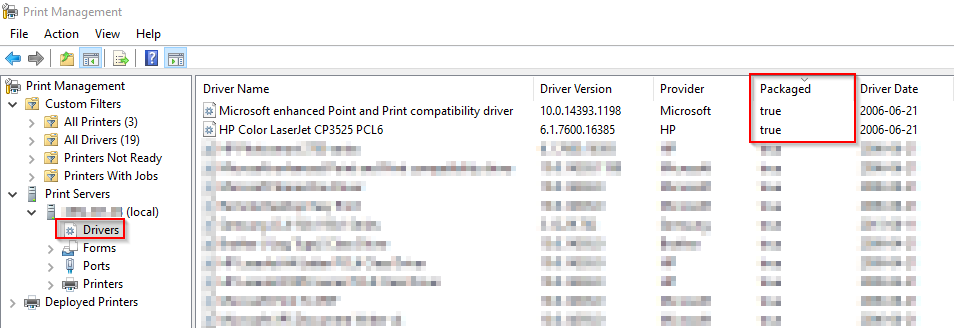
Since KB3170455 we need to enable point and print restrictions and specify our print servers in the GPO. For most printers there is no issues, however a couple of printers will not be pushed out by Group Policy Preferences since the update. Even though the print server was listed in the point and print GPO. Browsing the print share and trying to connect the printer manually would result in the ”Do you trust this printer” pop up which will then prompt for administrator credentials to install the driver. Looking at Print Management on the server in question shows that the problem printer drivers have a ”Packaged” status of false.
Workaround:
If you are pushing out printers via Group Policy or Group Policy Preferences and they are of Non-Packaged type you will always get a prompt to install, ignoring the point and print GPO, which will cause the install to fail. A workaround to this is a registry edit on the print server – test and verify this first before putting it into production:
- HKLM\System\CurrentControlSet\Control\Print\Enviroments\Windowsx64\Drivers\<…>\<Driver name>\PrinterDriverAttributes
Change the value from 0 to 1 and restart the printspool service or/and server. The value for other print drivers may not be 1, but to make this work the value needs to be set to an odd number. For example, if the value is 4 change it to 5. Only do these changes if you have no other means of getting a valid driver or printer swapped. In RDS/Citrix environments you could pre-install the printer driver on the host if viable and you only have a few session-hosts.
Back in Print Management you will see the Packaged status is now changed to true, and the printer should deploy. If you can find packaged print drivers then use those, but some manufacturers have not bothered supplying them.
Source: https://support.microsoft.com/en-us/help/3170005/ms16-087-security-update-for-windows-print-spooler-components-july-12
Personlig rådgivning
Vi erbjuder personlig rådgivning med författaren för 1400 SEK per timme. Anmäl ditt intresse i här så återkommer vi så snart vi kan.


Add comment