Posted in : Security Av Rickard Carlsson Översätt med Google ⟶
7 years ago
This year’s amazing conference Security Fest has now come to an end. Me and my colleague Sebastian had two really great days where we both have learned a lot and got new inspiration.
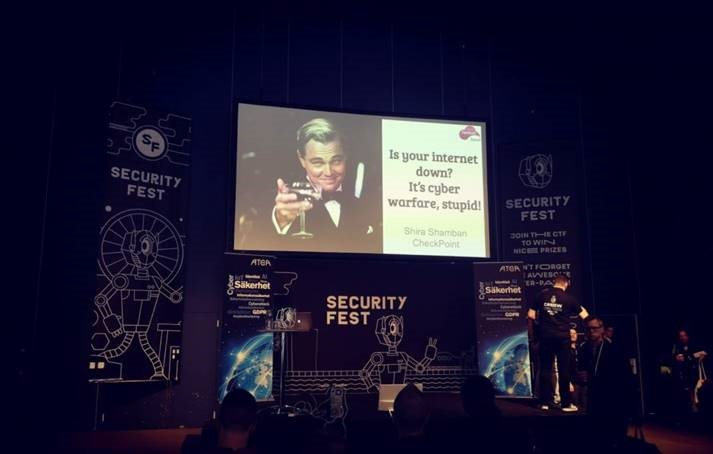
Picture from Shira Shamban’s talk – ”Your internet is down? It’s cyber warfare, stupid”
Christoffer Jerkeby – Load Balancer with RCE, Hacking F5
My favourite talk from this conference that I want to write a bit about was the super interesting talk by Christoffer Jerkeby about Remote Code Execution in F5’s Load Balancer, called Big-IP. Big-IP has a feature in the Local Traffic Manager that is called iRule which can be used to manage the network traffic. The language that is used for defining these iRules is a fork of the language TCL-8.4.
This language has a few flaws that are not well known and they are related to how the language expands variables and options. If the iRules are not written correctly, which they in many cases aren’t because the lack of knowledge of these flaws, the code will not work as expected to say the least.
Christoffer provided two demos to show how these flaws can be exploited. It can lead to MITM(Man-in-the-Middle), the ability to set and remove any HTTP header, intercept and inject user traffic for any session and termination of HTTPS.
Since the flaws are in how the language was built it’s not something that F5 can fix and no patch will or can be released that will mitigate this. This means that the people who configure these load balancers need to analyze their code in depth. It’s not easy to do that but Christoffer shared some great tools that can be used to help with the clean-up process and help you find out if your code is vulnerable.
You can find the tools and read more about them on github:
If you want to watch the whole presentation you can watch it from the link below. It will be well worth your time:
Other pictures from the conference:

Picture from Dave Lewis talk about the Zero Trust model. The talk was called “Zero Trust & The Flaming Sword of Justice!
Picture from Samit Anwer’s talk which was called “Oh! Auth: Implementation pitfalls of OAuth 2.0 & the Auth Providers who have fell in it”
Security Fest have uploaded all the presentations on their Youtube-channel so if you are interested you can watch these and all the other presentations from both days on their channel below:
If you have any other questions or want to know more, don’t hesitate to send me and email at: rickard.carlsson@xenit.se
Personlig rådgivning
Vi erbjuder personlig rådgivning med författaren för 1400 SEK per timme. Anmäl ditt intresse i här så återkommer vi så snart vi kan.


Add comment